Security Risk Action Items

In
order to conduct a Security Risk analysis, you need to complete 4 tasks:
- Conduct
a Risk Analysis
- Do
a Risk Management Assessment
- Implement
an Employee Sanction Policy
- Perform
a periodic system activity review
Most
likely you have already done all the above and they are safely tucked away in
the HIPAA and employee policy manuals, but if you are interested in more
details on this, see the overview section of this document. Otherwise, skip to
the following sections:
- Print out this document (particularly the Appendices A,
B, C and D)
- Keep your printout on file, in case of an audit
asking you to “prove that you did the security and risk analysis”
- Do the Risk Analysis, use Appendix A
- Read
each item, look at the default Office Medicine answers to each
question.
Add comments if desired (can leave it blank). Sign or initial, and date
each item (4th column).
- Do the Risk Management
Assessment,
use Appendix B
- This
has 4 sections. For each section, read each item, look at the default
Office
Medicine answers. Add comments if desired. Sign or initial, and date each
item (4th
column).
- Include an Employee
Sanction Policy in your employment policy documents. For guidance, you can use a
sample policy found in Appendix C
- Conduct a Periodic Audit. We suggest at least monthly,
but preferably weekly, you do the following:
- Look
at the Office Medicine audit log ( item #13 on the ONCMENU). See if there
are any irregularities, unauthorized access, or other issues.
- Fill
in a row in the Audit Log ( Appendix D), with the date of the review, the
name/initials of the reviewer, any findings (e.g. “none”), and actions
needed (e.g. “none”).
- Add
a new row with each audit. Weekly is suggested.
Once you’ve collected the above
information, you can Attest to having done a Privacy and Security Audit. Keep
your printouts in case of audits by CMS later on.
Overview

Introduction
Ensuring privacy and security of
electronic health information is:
·
Required by HIPAA,
·
addressed by
Office of the National Coordinator(ONC) via the Nationwide
Privacy and Security Framework for Electronic Exchange of
Individually Identifiable Health Information,
·
a Meaningful Use
requirement.
The
Meaningful Use objective is:
Protect electronic health information created or
maintained by the certified EHR technology through the implementation of
appropriate technical capabilities
The
specific Meaningful Use measure is:
Conduct or review a security risk analysis
per 45 CFR 164.308(a)(1) and implement security updates as necessary and
correct identified security deficiencies as part of its risk management
process.
There
are no exclusions to this measure. Everyone must conduct a review. The ONC has
published a resource, the Small
Practice Security Guide,
which can be helpful.
Security Risk Analysis rules
The security risk analysis specified
in the Meaningful Use measure is as follows:
45 CFR 164.308 - Administrative safeguards.
TITLE
45 - PUBLIC WELFARE
SUBTITLE A - DEPARTMENT OF HEALTH AND HUMAN
SERVICES CHAPTER I - SERVICES, GENERAL ADMINISTRATION
SUBCHAPTER C - ADMINISTRATIVE DATA
STANDARDS AND RELATED REQUIREMENTS PART 164 - SECURITY AND PRIVACY
subpart c - SECURITY STANDARDS FOR THE
PROTECTION OF ELECTRONIC PROTECTED HEALTH INFORMATION
164.308
- Administrative safeguards.
(a)
A covered entity must, in accordance with 164.306:
(1)
(i) Standard:
Security management process.
Implement policies and procedures to prevent, detect, contain, and
correct security violations.






Overview page 1
(ii) Implementation
specifications:
(A)
Risk analysis (Required). Conduct an
accurate and thorough assessment of the potential risks and
vulnerabilities to the confidentiality, integrity, and availability of
electronic protected health information held by the covered entity.
(B) Risk
management (Required). Implement security measures sufficient to
reduce risks and vulnerabilities to a reasonable and appropriate level
to comply with 164.306(a).
(C) Sanction policy (Required). Apply
appropriate sanctions against workforce members who fail to comply with the
security policies and procedures of the covered entity.
(D) Information system activity review
(Required). Implement procedures to regularly review records of information
system activity, such as audit logs, access reports, and security incident
tracking reports.
Office Medicine EHR
The
Office Medicine EHR is ONC-ACTB Certified for all the Certification
criteria associated with the Meaningful Use measure.
The
Certification criteria for this Meaningful Use Measure are as follows:
|
§170.302
(o)
|
Access
control
|
|
|
|
|
§170.302
(p)
|
Emergency
access
|
|
|
|
|
§170.302
(q)
|
Automatic
log-off
|
|
|
|
|
§170.302
(r)
|
Audit
log
|
|
|
|
|
§170.302 (s)
|
Integrity
|
|
|
|
|
§170.302
(t)
|
Authentication
|
|
|
|
|
§170.302
(u)
|
General
encryption
|
|
|
|
|
§170.302
(v)
|
Encryption
when exchanging electronic health information
|
|
|
|
By
using Office Medicine, many of the risks that a practice has with respect to
maintaining personal health information (PHI) are minimized.
Conducting a risk assessment
(Meaningful Use requirement)






Risk
analysis (Required). Conduct
an accurate and thorough assessment of the potential risks and
vulnerabilities to the confidentiality, integrity, and availability
of electronic protected health information held by the covered entity.
Definitions
of the terms in the regulation:
·
Confidentiality – the property that
electronic health information is not made available or disclosed to unauthorized
persons or processes.






·
Integrity – the property that
electronic health information have not been altered or destroyed in an unauthorized
manner.
·
Availability – the property that
electronic health information is accessible and useable upon demand by
an authorized person.
The
ONC
resource lists a series of “Questions to Ask Yourself” for
each of these areas – confidentiality, integrity and availability. These can be
assembled into a Checklist, and each item addressed – appended as Attachment A: Risk Analysis.
Reviewing
and checking answers to each of these items constitutes good-faith efforts to
demonstrate a security risk review, and will stand as evidence supporting
attestation of the Meaningful Use criterion. We suggest the practice print out
the attachments, check, sign and date them, and keep them for reference.





Risk management (Required). Implement
security measures sufficient to reduce risks and vulnerabilities to a
reasonable and appropriate level to comply with 164.306(a).
The
security standard referenced here is as follows:
164.306 - Security standards: General
rules.
(a)
General
requirements. Covered
entities must do the following:
(1) Ensure
the confidentiality, integrity, and availability of all electronic protected
health information the covered entity creates, receives, maintains, or
transmits.
(2) Protect
against any reasonably anticipated threats or hazards to the security or
integrity of such information.
(3) Protect
against any reasonably anticipated uses or disclosures of such information that
are not permitted or required under subpart E of this part.
(4)
Ensure
compliance with this subpart by its workforce.
The
ONC
resource lists a series of “Questions to Ask Yourself” around
identifying safeguards for electronic health information in the realms of:
·
Administrative
safeguards
·
Physical
safeguards
·
Technical safeguards
These
can be assembled into a Checklist, and each item addressed – appended as
Attachment B: Identifying
Safeguards.
Reviewing
and checking answers to each of these items constitutes good-faith efforts to
demonstrate a risk management review, and will stand as evidence supporting
attestation of the Meaningful Use criterion. We suggest the practice print out
the attachments, check, sign and date them, and keep them for reference.










 Sanction policy (Required). Apply appropriate sanctions against
workforce members who fail to comply with the security policies and
procedures of the covered entity.
Sanction policy (Required). Apply appropriate sanctions against
workforce members who fail to comply with the security policies and
procedures of the covered entity.
·
A practice
should create an employee policy with regards to implementing sanctions against
any failure to comply with the security policies identified above. A sample
policy is attached as Attachment C:
Sanction Policy (sample)
The
sample Sanction Policy is adapted from a brief
published by the American Health Information Management
Association (AHIMA) IN 2009.





Information system activity review (Required). Implement procedures to regularly
review records of information system activity, such as audit logs, access
reports, and security incident tracking reports.
·
A practice
should periodically review the Audit log contained in the Office Medicine
product, and document any findings. A sample record to document this review is
attached as Section D: Audit Log review



Attachment
A: Risk Analysis

|
Confidentiality
|
|
|
|
|
|
|
|
|
|
Question
|
OMNI
normal settings
|
Comments
|
Reviewed
|
|
|
|
|
|
|
What
new electronic health
|
Local
network-connected
|
|
|
|
information
has been introduced
|
computers
have no PHI on
|
|
|
|
into
my practice because of EHRs?
|
them.
The data is stored in a
|
|
|
|
Where
will that electronic health
|
secure
hosted environment
|
|
|
|
information
reside?
|
that
meets all the ONC-ACTB
|
|
|
|
|
criteria
|
|
|
|
|
|
|
|
|
Who
in my office (employees,
|
Those
designated as
|
|
|
|
other providers,
etc.) will have
|
Super Users will
create
|
|
|
|
access to EHRs,
and the electronic
|
access and set
permissions
|
|
|
|
health
information contained
|
for all other
users.
|
|
|
|
within them?
|
|
|
|
|
|
|
|
|
|
Should all
employees with access
|
Each employee in
a practice
|
|
|
|
to EHRs have the
same level of
|
has unique and
individual
|
|
|
|
access?
|
permissions, as
set by the
|
|
|
|
|
Administrator.
These
|
|
|
|

|
permissions
govern access
|
|
|
|
|
available to the
user.
|
|
|
|
|
|
|
|
|
Will I permit my
employees to
|
No Internet-connected
|
|
|
|
have electronic
health information
|
computer or
device houses
|
|
|
|
on mobile
computing/storage
|
PHI locally.
There is no local
|
|
|
|
equipment? If so,
do they know
|
data to keep
secure.
|
|
|
|
how, and do they
have the
|
Exception: scanned
|
|
|
|
resources necessary,
to keep
|
documents will be
created on
|
|
|
|
electronic health
information
|
local computers,
that need
|
|
|
|
secure
on these devices?
|
uploading
to the EHR
|
|
|
|
|
system.
Once uploaded, the
|
|
|
|
|
local
copy of these scanned
|
|
|
|
|
image files are deleted.
|
|
|
|
|
|
|
|
|
|
|
|
|
|
How
will I know if electronic
|
A
designated person in the
|
|
|
|
health
information has been
|
practice can
review the Audit
|
|
|
|
accidentally or
maliciously
|
Log for the
practice, or for a
|
|
|
|
disclosed to an
unauthorized
|
specific patient,
at any time.
|
|
|
|
person?
|
|
|
|
|
|
|
|
|









































When
I upgrade my computer
|
With
a server-based EHR, no
|
|
|
|
storage
equipment (e.g., hard
|
PHI
is stored locally except on the secure server database.
|
|
|
|
drives),
will electronic health
|
Upgrading
local machines
|
|
|
|
information
be properly erased
|
does
not leave any PHI
|
|
|
|
from
the old storage equipment
|
exposed.
|
|
|
|
before
I dispose of it?
|
|
|
|
|
|
|
|
|
|
Are
my backup facilities secured
|
The server
based EHR manages the cloud
|
|
|
|
(computers,
tapes, offices, etc.,
|
Based
backup by using the encrypted I-Drive system. Additional local backups
are also recommended.
|
|
|
|
used
to backup EHRs and other
|
|
|
|
|
health
IT)?
|
|
|
|
|
|
|
|
|
|
Will
I be sharing EHRs, or
|
Data
that is shared through a
|
|
|
|
electronic
health information
|
Health
Information Exchange
|
|
|
|
contained
in EHRs with other
|
will
be via security policies
|
|
|
|
health
care entities through a
|
stated
in the product, and
|
|
|
|
HIE? If so, what
security policies
|
which much be
agreed to in
|
|
|
|
do I need to be
aware of?
|
order to access
these
|
|
|
|
|
services.
|
|
|
|
|
|
|
|
|
If my EHR system
is capable of
|
The entire Office
Medicine
|
|
|
|
providing my
patients with a way
|
EHR platform is
ONC-ACTB
|
|
|
|
to access their
health
|
Certified to meet
all the
|
|
|
|
record/information
via the
|
security and
data-exchange
|
|
|
|
Internet (e.g.,
through a portal),
|
standards
specified. The
|
|
|
|
am I
familiar with the security
|
connected
Patient Portal
|
|
|
|
requirements that
will protect my
|
utilizes the same
|
|
|
|
patients
electronic health
|
level of
encryption,
|
|
|
|
information
before I implement
|
authentication,
and integrity-
|
|
|
|
that feature?
|
checking that the
EHR does.
|
|
|
|
|
|
|
|
|
Will I
communicate with my
|
Patient
communications
|
|
|
|
patients
electronically (e.g.,
|
through the
linked Patient
|
|
|
|
through a portal
or email)? Are
|
Portal platform is
secured.
No PHI will be
|
|
|
|
those
communications secured?
|
exposed through
|
|
|
|
|
unsecured
email.
|
|
|
|
|
|
|
|
|
If I offer my
patients a method of
|
Patient
authentication on
|
|
|
|
communicating
with me
|
login
to the Portal identifies
|
|
|
|
electronically,
how will I know that
|
the
patient uniquely.
|
|
|
|
I am
communicating with the right
|
Communication
of any
|
|
|
|
patient?
|
messages
from/to this
|
|
|
|
|
patient
is ensured by the
|
|
|
|
|
tight EHR-Portal
linkage.
|
|
|
|
|
|
|
|






|
Integrity
|
|
|
|
|
|
|
|
|
|
Question
|
OMNI
normal settings
|
Comments
|
Reviewed
|
|
|
|
|
|
|
Who
in my office will be permitted
|
The
clinician can create and
|
|
|
|
to
create or modify an EHR, or
|
edit
chart notes. Once
|
|
|
|
electronic
health information
|
signed,
no one can alter
|
|
|
|
contained
in the EHR?
|
them,
though addenda can
|
|
|
|
|
be
appended.
|
|
|
|
|
|
|
|
|
How
will I know if an EHR, or the
|
All
activity in a chart is
|
|
|
|
electronic
health information in
|
recorded
in an Audit Log,
|
|
|
|
the
EHR, has been altered or
|
which
is a plain-English
|
|
|
|
deleted?
|
record
of access,
|
|
|
|
|
modification
and deletion of
|
|
|
|
|
data in a chart.
|
|
|
|
|
|
|
|
|
If I participate
in a HIO, how will I
|
External data
imported into
|
|
|
|
know
if the health information I
|
the
EHR is kept separately
|
|
|
|
exchange is
altered in an
|
from in-practice
created
|
|
|
|
unauthorized
manner?
|
data. All data,
in-house and
|
|
|
|
|
imported, is
tracked in the
|
|
|
|
|
Audit Log
|
|
|
|
|
|
|
|
|
If my EHR system
is capable of
|
Clinician-created
data, and
|
|
|
|
providing my
patients with a way
|
patient-created
data are kept
|
|
|
|
to access their
health
|
separately. All
activity,
|
|
|
|
record/information
via the
|
whether
clinician-created or
|
|
|
|
Internet (e.g.,
through a portal)
|
patient-created,
is tracked in
|
|
|
|
and I implement
that feature, will
|
the Audit Log.
|
|
|
|
my patients be
permitted to
|
|
|
|
|
modify
any of the health
|
|
|
|
|
information
within their record? If
|
|
|
|
|
so, what
information?
|
|
|
|
|
|
|
|
|





































|
Availability
|
|
|
|
|
|
|
|
|
|
Question
|
Omni
normal settings
|
Comments
|
Reviewed
|
|
|
|
|
|
|
How
will I ensure that electronic
|
With
a server-based EHR,
|
|
|
|
health
information, regardless of
|
access
can be achieved from
|
|
|
|
where
it resides, is readily
|
any
Internet-connected
|
|
|
|
available
to me and my employees
|
computer,
from any location,
|
|
|
|
for
authorized purposes, including
|
at
any time. No locally-
|
|
|
|
after
normal office hours?
|
installed
client software is
|
|
|
|
|
needed.
No VPN or other
|
|
|
|
|
special
connectivity is
|
|
|
|
|
needed.
|
|
|
|
|
|
|
|
|
Do I
have a backup strategy for my
|
Since
the EHR is hosted on
|
|
|
|
EHRs in the event
of an
|
commercial-grade
secure
|
|
|
|
emergency,
or to ensure I have
|
servers,
up-time is ensured
|
|
|
|
access to patient
information if
|
per the Service
Level
|
|
|
|
the power goes
out or my
|
Agreement. Any
local
|
|
|
|
computer crashes?
|
computer can be
used to
|
|
|
|
|
access this
service, and local
|
|
|
|
|
computer failure
can be
|
|
|
|
|
interchanged with
any other
|
|
|
|
|
computer.
|
|
|
|
|
|
|
|
|
If I participate
in a HIO, does it
|
The Office
Medicine server
|
|
|
|
have performance
standards
|
hosting system is
run on
|
|
|
|
regarding network
availability?
|
commercial-grade
servers,
|
|
|
|
|
protected
by a Service Level
|
|
|
|
|
Agreement.
|
|
|
|
|
|
|
|
|
If my EHR system
is capable of
|
Patient access to
their Portal is server based and available
|
|
|
|
providing my
patients with a way
|
24/7.
|
|
|
|
to access their
health
|
|
|
|
|
record/information
via the
|
Any secure
communication
|
|
|
|
Internet
(e.g., through a portal)
|
between
the clinician and
|
|
|
|
and I
implement that feature, will I
|
patient
will have response
|
|
|
|
allow
24/7 access?
|
expectations
set by
|
|
|
|
|
notifications
within the
|
|
|
|
|
product.
|
|
|
|
|
|
|
|





































Attachment
B: Identifying Safeguards

|
Administrative
safeguards
|
|
|
|
|
|
|
|
|
|
Question
|
OMNI normal settings
|
Comments
|
Reviewed
|
|
|
|
|
|
|
Have
I updated my internal
|
Periodic
review of the Risk
|
|
|
|
information
security processes to
|
Analysis,
with comments and
|
|
|
|
include
the use of EHRs,
|
check
/ sign / date of each
|
|
|
|
connectivity
to HIOs, offering
|
item
accomplishes this.
|
|
|
|
portal
access to patients, and the
|
|
|
|
|
handling
and management of
|
|
|
|
|
electronic
health information in
|
|
|
|
|
general?
|
|
|
|
|
|
|
|
|
|
Have I trained my
employees on
|
Each user
undergoes training
|
|
|
|
the use of EHRs?
Other electronic
|
within the
product, and can
|
|
|
|
health
information related
|
elect to engage
online
|
|
|
|
technologies that
I plan to
|
training and
support with
|
|
|
|
implement? Do
they understand
|
Office Medicine
(offered
|
|
|
|
the
importance of keeping
|
free).
|
|
|
|
electronic health
information
|
Employee sanction
policy is
|
|
|
|
protected?
|
reviewed with
each
|
|
|
|
|
employee, and
placed in
|
|
|
|
|
personnel record.
|
|
|
|
|
|
|
|
|
Have I identified
how I will
|
Establish
periodicity by in-
|
|
|
|
periodically
assess my use of
|
house policy, and
conduct
|
|
|
|
health IT to
ensure my safeguards
|
review of
Identifying
|
|
|
|
are effective?
|
Safeguards. Check
/ sign /
|
|
|
|
|
date each item to
document
|
|
|
|
|
this.
|
|
|
|
|
|
|
|
|
As
employees enter and leave my
|
Practice
Administrator will
|
|
|
|
practice,
have I defined processes
|
manage
the user list within
|
|
|
|
to
ensure electronic health
|
the
EHR, and will de-activate
|
|
|
|
information
access controls are
|
access to former
employees.
|
|
|
|
updated
accordingly?
|
|
|
|
|
|
|
|
|









































|
Have
I developed a security
|
Only
one instance of a user’s
|
|
|
|
incident
response plan so that my
|
login
is supported at a time,
|
|
|
|
employees
know how to respond
|
so
any login using stolen
|
|
|
|
to a
potential security incident
|
credentials
can be identified.
|
|
|
|
involving
electronic health
|
If
EHR access using stolen
|
|
|
|
information
(e.g., unauthorized
|
credentials
is identified, the
|
|
|
|
access
to an EHR, corrupted
|
practice
will:
|
|
|
|
electronic
health information)?
|
1.
Reset the password for
|
|
|
|
|
that
user, or de-activate
|
|
|
|
|
that
user
|
|
|
|
|
2.
Review the Audit Logs to
|
|
|
|
|
identify
patients
|
|
|
|
|
accessed
by that user
|
|
|
|
|
3.
Notify the patients
|
|
|
|
|
whose
records were
|
|
|
|
|
breached
within 30
|
|
|
|
|
days, in
compliance with
|
|
|
|
|
HIPAA
standards
|
|
|
|
|
|
|
|
|
Have I developed
processes that
|
The hosted EHR
can store
|
|
|
|
outline how
electronic health
|
patient
information ad
|
|
|
|
information will
be backed-up or
|
infinitum, and manages all
|
|
|
|
stored outside of
my practice
|
backup. No local
backup is
|
|
|
|
when it is no
longer needed (e.g.,
|
needed.
|
|
|
|
when a patient
moves and no
|
Patients can be
flagged as
|
|
|
|
longer receives
care at the
|
Inactive, as
needed.
|
|
|
|
practice)?
|
|
|
|
|
|
|
|
|
|
Have I developed
contingency
|
Since the EHR is server-based,
|
|
|
|
plans so that my
employees know
|
Internet connectivity
is
|
|
|
|
what to do if
access to EHRs and
|
required. If
there is a lapse in
|
|
|
|
other electronic
health
|
Internet
connection from the
|
|
|
|
information
is not available for an
|
main
source, alternate
|
|
|
|
extended period
of time?
|
methods of access
will be
|
|
|
|
|
implemented (e.g.
wireless
|
|
|
|
|
cell phone
access), as
|
|
|
|
|
technology
allows.
|
|
|
|
|
|
|
|
|
Have I developed
processes for
|
External
electronic data
|
|
|
|
securely
exchanging electronic
|
exchange will
occur only
|
|
|
|
health
information with other
|
through the
channels
|
|
|
|
health
care entities?
|
allowed
within the product.
|
|
|
|
|
Security
for this exchange is
|
|
|
|
|
documented
within the
|
|
|
|
|
product,
and referenced in
|
|
|
|
|
the Licencing
Agreements.
|
|
|
|
|
|
|
|






|
Have
I developed processes that
|
Patient
access to their PORTAL is
|
|
|
|
my
patients can use to securely
|
granted
one-at-a-time, via
|
|
|
|
connect
to a portal? Have I
|
verified
patient email. One of
|
|
|
|
developed
processes for proofing
|
the
three credentials needed
|
|
|
|
the
identity of my patients before
|
for
patient access is given to
|
|
|
|
granting
them access to the
|
the
patient in-person, and
|
|
|
|
portal?
|
the
remaining two
|
|
|
|
|
credentials
are emailed. The
|
|
|
|
|
patient
must then change
|
|
|
|
|
his/her
password upon first
|
|
|
|
|
usage.
|
|
|
|
|
|
|
|
|
Do I
have a process to periodically
|
Office
Medicine is server-
|
|
|
|
test
my health IT backup
|
hosted
on commercial-grade
|
|
|
|
capabilities,
so that I am prepared
|
secured
servers. Data backup
|
|
|
|
to execute them?
|
is done
centrally, and no
|
|
|
|
|
local backup of
data is
|
|
|
|
|
needed.
|
|
|
|
|
|
|
|
|
If equipment is
stolen or lost, have
|
Since no PHI is
contained on
|
|
|
|
I defined
processes to respond to
|
local computers,
the loss or
|
|
|
|
the theft or
loss?
|
theft of
equipment is simply
|
|
|
|
|
property
loss. Property loss is
|
|
|
|
|
managed through
routine
|
|
|
|
|
theft-and-loss
processes (e.g.
|
|
|
|
|
police reporting,
insurance
|
|
|
|
|
reporting).
|
|
|
|
|
|
|
|






|
Physical safeguards
|
|
|
|
|
|
|
|
|
|
Question
|
OMNI
normal settings
|
Comments
|
Reviewed
|
|
|
|
|
|
|
Do I
have basic office security in
|
Practice
manager to address
|
|
|
|
place,
such as locked doors and
|
and
verify this.
|
|
|
|
windows,
and an alarm system?
|
|
|
|
|
Are
they being used properly
|
|
|
|
|
during
working and non-working
|
|
|
|
|
hours?
|
|
|
|
|
|
|
|
|
|
Are
my desktop computing
|
Office
Medicine implements
|
|
|
|
systems
in areas that can be
|
auto-logoff
after a period of
|
|
|
|
secured
during non-working
|
inactivity.
However, the
|
|
|
|
hours?
|
entire
computer desktop
|
|
|
|
|
should
be Locked at the end
|
|
|
|
|
of a work
session.
|
|
|
|
|
|
|
|
|
Are my desktop
computers out of
|
Verify physical
location of
|
|
|
|
the
reach of patients and other
|
computers,
make sure
|
|
|
|
personnel not
employed by my
|
screens are not
visible by
|
|
|
|
practice during
normal working
|
those not working
at the
|
|
|
|
hours?
|
station.
|
|
|
|
|
|
|
|
|
Is mobile
equipment (e.g.,
|
Office Medicine
implements
|
|
|
|
laptops), used
within and outside
|
auto-logoff after
a period of
|
|
|
|
my office,
secured to prevent theft
|
inactivity. Upon
leaving the
|
|
|
|
or loss?
|
premises,
computers should
|
|
|
|
|
be shut down or
hibernated,
|
|
|
|
|
with password
re-launch
|
|
|
|
|
required.
|
|
|
|
|
|
|
|
|
Do I have a
documented inventory
|
With Office
Medicine, any
|
|
|
|
of approved and
known health IT
|
Internet-connected
|
|
|
|
computing
equipment within my
|
computer
can be used to
|
|
|
|
practice? Will I
know if one of my
|
connect to the
EHR. Per-user
|
|
|
|
employees is
using a computer or
|
access
(regardless of physical
|
|
|
|
media
device not approved for my
|
machine
or location) is
|
|
|
|
practice?
|
captured
in the Audit Log.
|
|
|
|
|
It is
good business practice to
|
|
|
|
|
inventory
in-house
|
|
|
|
|
equipment,
and is advised.
|
|
|
|
|
|
|
|
|
Do my
employees implement basic
|
Office
Medicine implements
|
|
|
|
computer
security principles, such
|
auto-logoff
after a period of
|
|
|
|
as
logging out of a computer
|
inactivity.
However, the
|
|
|
|
before leaving it
unattended?
|
entire computer
desktop
|
|
|
|
|
should
be Locked at the end
|
|
|
|
|
of a work
session.
|
|
|
|
|
|
|
|





































|
Technical safeguards
|
|
|
|
|
|
|
|
|
|
Question
|
OMNI
normal settings
|
Comments
|
Reviewed
|
|
|
|
|
|
|
Have
I configured my computing
|
The Office
Medicine EHR
|
|
|
|
environment
where electronic
|
maintains
security on the
|
|
|
|
health
information resides using
|
server.
There is no local PHI.
|
|
|
|
best-practice
security settings
|
|
|
|
|
(e.g.,
enabling a firewall, virus
|
Exception: local copies of
|
|
|
|
detection,
and encryption where
|
scanned-document
files, and
|
|
|
|
appropriate)?
Am I maintaining
|
local
copies of Reports that
|
|
|
|
that
environment to stay up to
|
may
have been output may
|
|
|
|
date
with the latest computer
|
contain
PHI. They should
|
|
|
|
security
updates?
|
1.
Be deleted when
|
|
|
|
|
finished
with them
|
|
|
|
|
2.
Should only be on
|
|
|
|
|
machines with
up-to-
|
|
|
|
|
date antivirus
and
|
|
|
|
|
firewall software
|
|
|
|
|
installed
|
|
|
|
|
3. If these
files are to
|
|
|
|
|
remain on a local
|
|
|
|
|
machine, the
files
|
|
|
|
|
should be
encrypted
|
|
|
|
|
|
|
|
|
Are their other
types of software
|
Since Office
Medicine is
|
|
|
|
on my
electronic health
|
accessed
through a simple
|
|
|
|
information computing
equipment
|
server browser,
and no local
|
|
|
|
that are not
needed to sustain my
|
PHI resides on
the client
|
|
|
|
health IT
environment (e.g., a
|
machine, there is
no
|
|
|
|
music file
sharing program), which
|
limitation to
other software
|
|
|
|
could put my
health IT
|
that may reside
on that client
|
|
|
|
environment at
risk?
|
machine.
|
|
|
|
|
|
|
|
|
Is my EHR
certified to address
|
Office Medicine
is ONC-ACTB
|
|
|
|
industry
recognized/best-practice
|
Certified
to conform to
|
|
|
|
security
requirements?
|
industry
recognized best-
|
|
|
|
|
practice with
respect to
|
|
|
|
|
security.
|
|
|
|
|
|
|
|
|
Are my health IT
applications
|
Only a server
browser (any
|
|
|
|
installed
properly, and are the
|
browser, any
platform) with
|
|
|
|
vendor
recommended security
|
an
Internet connection is
|
|
|
|
controls enabled
(e.g., computer
|
required for Office
Medicine.
|
|
|
|
inactivity
timeouts)?
|
|
|
|
|
|
|
|
|





































|
Is my
health IT computing
|
Up to
date security on any
|
|
|
|
environment
up to date with the
|
local
client machine is
|
|
|
|
most
recent security updates and
|
advised.
However, access to
|
|
|
|
patches?
|
PHI
via the Office Medicine
|
|
|
|
|
server
browser is secured by
|
|
|
|
|
the
server and forces the
|
|
|
|
|
browser
to implement secure
|
|
|
|
|
communication
methods.
|
|
|
|
|
|
|
|
|
Have
I configured my EHR
|
Office
Medicine requires 3-
|
|
|
|
application
to require my
|
key
authentication, unique
|
|
|
|
employees
to be authenticated
|
for
each user, in order to
|
|
|
|
(e.g.,
username/password) before
|
access
the system. Only one
|
|
|
|
gaining
access to the EHR? And
|
such
session can be active at
|
|
|
|
have
I set their access privileges to
|
any
given time.
|
|
|
|
electronic health
information
|
The Practice
Administrator
|
|
|
|
correctly?
|
sets (and edits)
permissions
|
|
|
|
|
for each user in
the practice
|
|
|
|
|
|
|
|
|
If I have or plan
to establish a
|
Patient access to
the portal is
|
|
|
|
patient portal,
do I have the
|
granted
one-at-a-time, via
|
|
|
|
proper security
controls in place to
|
verified patient
email. One of
|
|
|
|
authenticate
the patient (e.g.,
|
the
three credentials needed
|
|
|
|
username/password)
before
|
for patient
access is given to
|
|
|
|
granting access
to the portal and
|
the patient
in-person, and
|
|
|
|
the patient’s
electronic health
|
the remaining two
|
|
|
|
information? Does
the portal’s
|
credentials are
emailed. The
|
|
|
|
security reflect
industry best-
|
patient must then
change
|
|
|
|
practices?
|
his/her password
upon first
|
|
|
|
|
usage.
|
|
|
|
|
The portal uses
the same
|
|
|
|
|
secure
server system
|
|
|
|
|
that the Office
Medicine EHR
|
|
|
|
|
uses, and is
certified to
|
|
|
|
|
conform to the
same level of
|
|
|
|
|
privacy and
security that the
|
|
|
|
|
EHR
implements
|
|
|
|
|
|
|
|






|
If I
have or plan to set up a
|
Since
the Office Medicine EHR
|
|
|
|
wireless
network, do I have the
|
is server
based, all access is
|
|
|
|
proper
security controls defined
|
secured
over the Internet.
|
|
|
|
and
enabled (e.g., known access
|
Local
in-house wireless
|
|
|
|
points,
data encryption)?
|
access
is no different than
|
|
|
|
|
access
from home, or
|
|
|
|
|
elsewhere,
and needs no
|
|
|
|
|
extra
security layer in order
|
|
|
|
|
to
achieve a secure
|
|
|
|
|
connection.
|
|
|
|
|
|
|
|
|
Have
I enabled the appropriate
|
Periodic
review of the Audit
|
|
|
|
audit
controls within my health IT
|
Log
will be implemented and
|
|
|
|
environment
to be alerted of a
|
documented.
|
|
|
|
potential
security incident, or to
|
|
|
|
|
examine security
incidents that
|
|
|
|
|
have occurred?
|
|
|
|
|
|
|
|
|






Attachment C: Sanction Policy (example)

Medical
practice name: ____________________________________________________
It is in the best interest of the
healthcare industry generally, and this practice in particular, to address the
issue of securing the Privacy and Security of individually-identifiable health
information in a proactive manner through implementation of sanction practice
standards. Aside from the necessity to ensure patient privacy as an ethical
obligation, it is smart business. Data breach notification laws in more than 40
states require an organization to notify breach victims, which can damage its
reputation.
Privacy Incident categories:
The practice defines categories that define
the significance and impact of the privacy or security incident to help guide
corrective action and remediation.
·
Category 1: Unintentional breach of
privacy or security that may be caused by carelessness, lack of
knowledge, or lack of judgment, such as a registration error that causes a
patient billing statement to be mailed to the wrong guarantor.
·
Category 2a: Deliberate unauthorized
access to PHI without PHI disclosure. Examples: snoopers accessing
confidential information of a VIP, coworker, or neighbor without legitimate
business reason; failure to follow policy without legitimate reason, such as
password sharing.
·
Category 2b: Deliberate unauthorized
disclosure of PHI or deliberate tampering with data without malice or
personal gain. Examples: snooper access and redisclosure to the news media;
unauthorized modification of an electronic document to expedite a process.
·
Category 3: Deliberate unauthorized
disclosure of PHI for malice or personal gain. Examples: selling
information to the tabloids or stealing individually identifiable health
information to open credit card accounts.
Factors that may modify application of sanctions:
Sanctions may be modified based on
mitigating factors. Factors may reflect greater damage caused by the breach and
thus work against the offender and ultimately increase the penalty.
Examples include:
·
Multiple
offenses
·
Harm
to the breach victim(s)
·
Breach
of specially protected information such as HIV-related, psychiatric, substance
abuse, and genetic data
·
High
volume of people or data affected
·
High
exposure for the institution
·
Large
organizational expense incurred, such as breach notifications
·
Hampering
the investigation
·
Negative
influence of actions on others






Factors
that could mitigate sanctioning could include:
·
Breach
occurred as a result of attempting to help a patient
·
Victim(s)
suffered no harm
·
Offender
voluntarily admitted the breach and cooperated with the investigation
·
Offender
showed remorse
·
Action
was taken under pressure from an individual in a position of authority
·
Employee
was inadequately trained
Sanction process
The HIPAA regulations require that imposed
sanctions be consistent across the board irrespective of the status of the
violator, with comparable discipline imposed for comparable violations. This
practice will enable application of general principles that will lead to fair and
consistent outcomes.
Sanction implementation will follow the
following steps. However, depending on the Category level of the incident, an
escalated process can be followed if cause is shown:
·
Documented
conference with recommendations for additional, specific, documented training,
if necessary
·
First
written warning (and training, as above, if warranted)
·
Final
warning, with or without suspension, with or without pay (training included, if
warranted)
·
Severance
of formal relationship: employment, contract, medical staff privileges,
volunteer status






Attachment
D: Audit Log review

|
Audit Log Review
|
|
|
|
|
|
|
|
|
|
Date
Audit Log was
|
Name
of reviewer
|
Findings
|
Action
needed
|
|
reviewed
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|




































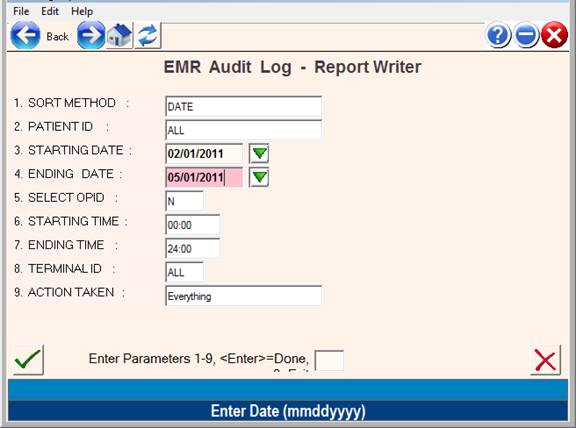
To obtain
the Audit Log Report, select item 13 on the ONCMENU
Example Audit Log from Office Medicine:
Step #1: From the main menu type: ONCMENU <Enter>
Step #2: Select #13
Step #3: Enter Dates:
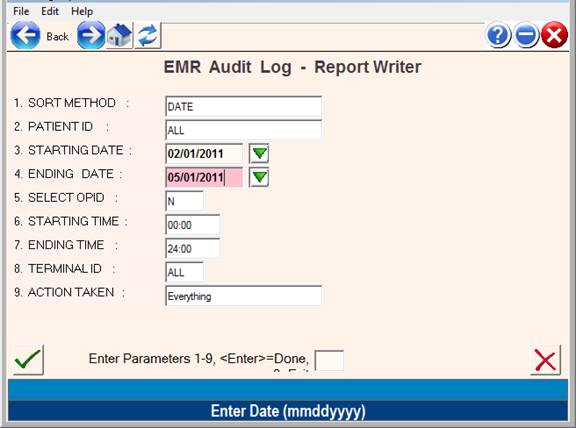
Step #4: Review Report for actions items.
Example Report
04:24:24 PM EMR AUDIT LOG
SORTED REPORT PAGE: 0001
05/01/2011 PERIOD: 02012011 -
05012011 SORT: PGM: EMRHLOG
OPID:OMNI VER:
12
Florida Family
Allergy Center PLC
PATIENT ID NAME DATE TIME
ACTION FIELD OPID TERM
__________________________________________________________________________________
000140 ADAMS, LATISHA 02042011 93740
Added UCG OMNI T000
000140 ADAMS, LATISHA 02042011 93854
Deleted UCG OMNI T000
000140 ADAMS, LATISHA 02042011 93900
Deleted VS OMNI T000
000140 ADAMS, LATISHA 02042011 100151
Added VS OMNI T000
000010 MILLER-LYNN,
LINDA02072011 120938 Added CC OMNI T000
000010 MILLER-LYNN,
LINDA02072011 121005 Updated CC OMNI T000
000010 MILLER-LYNN,
LINDA02072011 121016 Added HPI OMNI T000
000010 MILLER-LYNN,
LINDA02072011 121027 Deleted PMH OMNI T000
000010 MILLER-LYNN,
LINDA02072011 121033 Added EXAM OMNI T000
000420 MEMMINGER, BARBARA02072011
121154 Deleted PMH OMNI T000
000420 MEMMINGER, BARBARA02072011 121201
Added EXAM OMNI T000
000430 WILKINSON, FRANK 02072011 121852
Added PMH OMNI T000
000430 WILKINSON, FRANK 02072011 121908
Updated PMH OMNI T000
000430 WILKINSON, FRANK 02072011 121946
Deleted PMH OMNI T000
000570 JOHNSON, PHILIP 02072011 122153
Viewed PLAB OMNI T000
000430 WILKINSON, FRANK 02072011 123444
Deleted PKC OMNI T000
000430 WILKINSON, FRANK 02072011 123500
Deleted PKC OMNI T000
000430 WILKINSON, FRANK 02072011 123533
Deleted EXAM OMNI T000
000570 JOHNSON, PHILIP 02072011 123634 Deleted
PLAB OMNI T000
000570 JOHNSON, PHILIP 02072011 123702
Added PLAB OMNI T000
000570 JOHNSON, PHILIP 02072011 123723
Added PLAB OMNI T000
000430 WILKINSON, FRANK 02072011 125359
Added PLAB OMNI T000
000430 WILKINSON, FRANK 02072011 125532
Updated CC OMNI T000
000430 WILKINSON, FRANK 02072011 125543
Added HPI OMNI T000
000430 WILKINSON, FRANK 02072011 125552
Viewed CC OMNI T000
000430 WILKINSON, FRANK 02072011 125607
Added VS OMNI T000
000430 WILKINSON, FRANK 02072011 125611
Added PF1 OMNI T000
000430 WILKINSON, FRANK 02072011 125612
Viewed CC OMNI T000
000430 WILKINSON, FRANK 02072011 125629
Viewed CC OMNI T000
000430 WILKINSON, FRANK 02072011 125842
Updated VS OMNI T000
000430 WILKINSON, FRANK 02072011 125933
Updated HPI OMNI T000
Example Audit Review Action:
Operator OMNI should not be
allowed Delete permission.
![]()